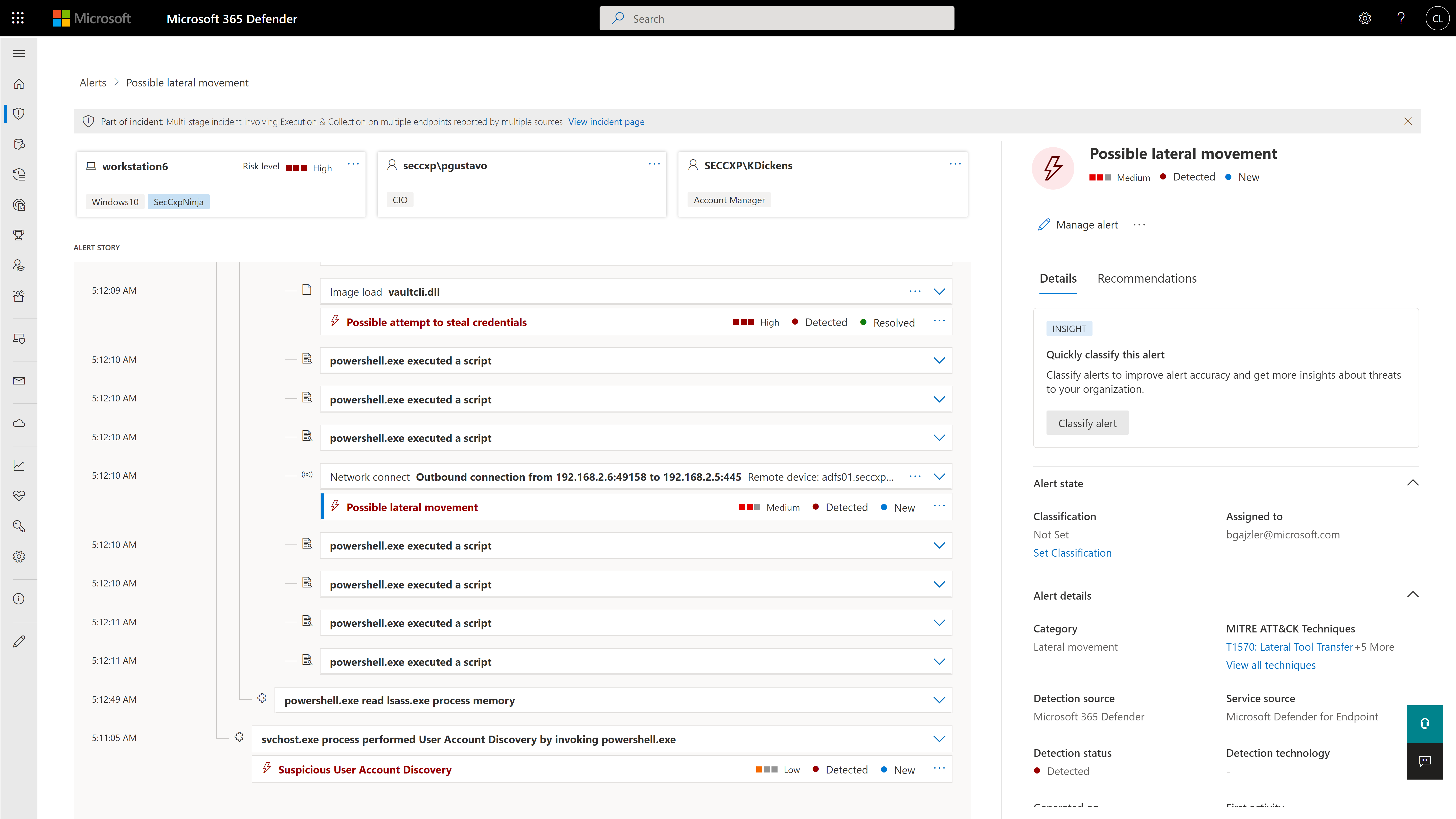
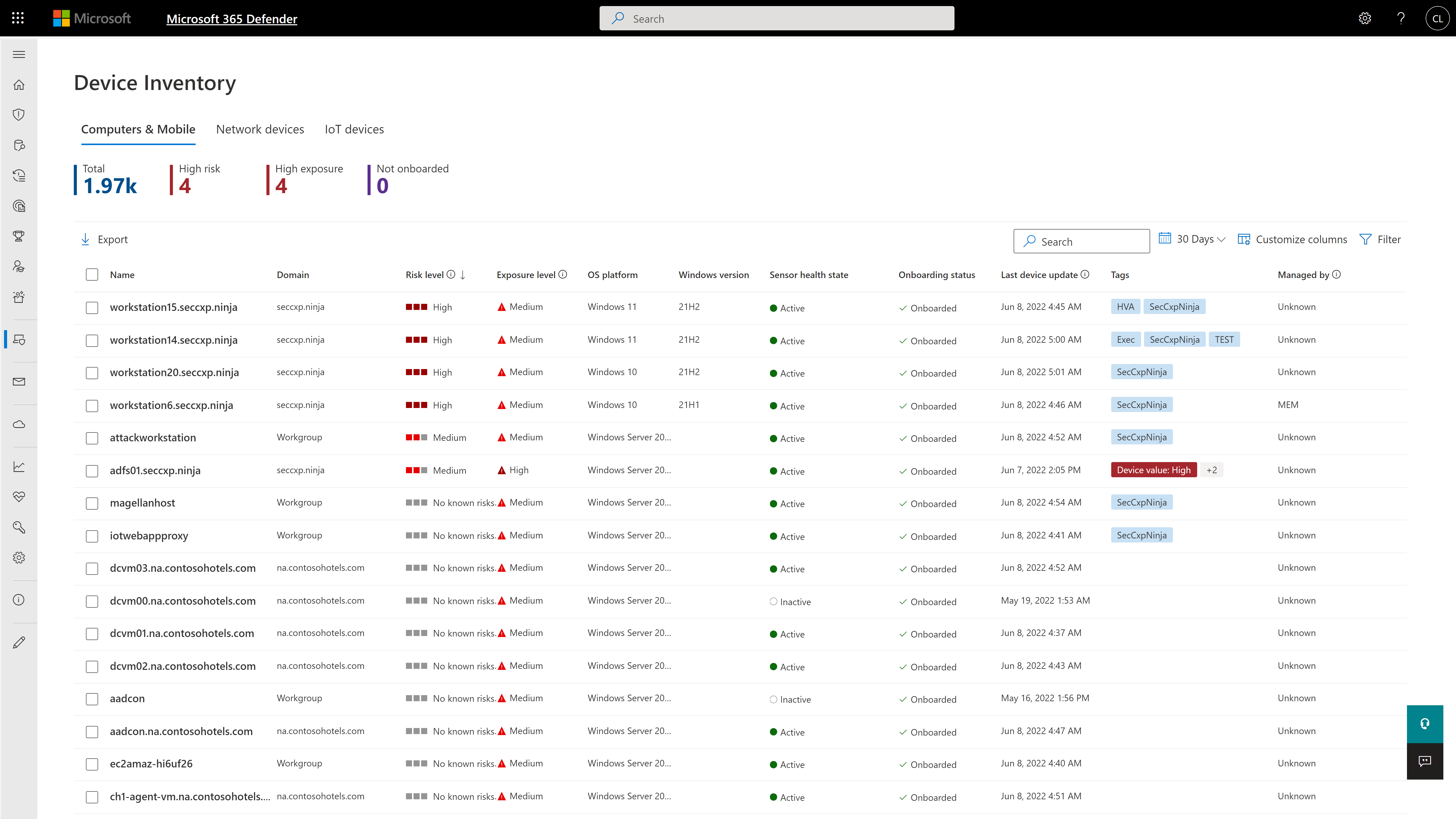
Microsoft Defender for Endpoint
Use Cases and Deployment Scope
Pros
- I get a good rest. Static file Detections of malware are updated quite often and are also quite effective. And overall has more.
Cons
- So far, it has not been detecting the link. File. Malware for changes that we are facing where you buy separately from simple anti, let the link file malware problem.
Return on Investment
- It's malware detection, so it didn't apply any objectively; it didn't really apply any bit objectively is anti-slideshare.